2 July, 2018 - We are all increasingly aware of the threats our businesses face in this world of internet and communications. Some are quite well known (viruses, malware, etc.) that depend, more or less, on an uncontrolled use of our PCs. But there are also others that are based on new strategies that take advantage of weaknesses in the operating systems and/or communications routers we have in our offices.
So now it is no longer just a matter of making employees aware not to access unfamiliar websites or open unknown emails. We also have to be prepared for attacks by cybercriminals on our office computers.
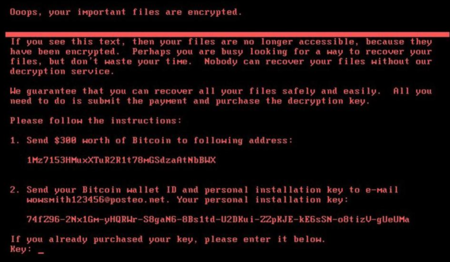
These "cyber-attacks" can enter our companies and "hijack" information. Moreover, if they only enter one computer, the infection can spread to all computers in the network or even to all employees in the company! Some famous attacks are those produced by "ramsonware" threats in which the user's data is encrypted and a ransom is demanded, usually in bitcoins, in order to recover the information. Examples of these cases are the well-known WannaCry and NotPetya that attacked last year all over the world (including large companies in our country).

Another type of threat that has been growing significantly over the last year is cryptojacking. In this case, instead of stealing information from users' files, what is stolen here are CPU cycles from the infected machine to "mine" cryptocurrencies. This is why this threat is more subtle, as the user may be infected and not know it.
Multiple other threats are occurring, such as those stemming from the theft of government (NSA) hacking tools.
We are in a wild world. Both trying to stay ahead. SW/HW manufacturers making products more secure and the "bad guys" looking for weaknesses. But the problem is that most companies lack specialised resources to be able to control these threats from entering their networks. Even more so when they have different offices or branches. Each one can become a point of attack for cybercriminals.
Hence the emergence of state-of-the-art "firewall" protection solutions such as Untangle's. These solutions consist of installing equipment that acts as a barrier against bad traffic or cyber-attacks. These solutions consist of installing equipment that acts as a barrier against bad traffic or cyber-attacks.
Among other things, these devices have "real-time" information about what is happening on the internet and can identify "malicious" IP addresses. In this situation, firewalls block the data coming from these addresses and thus prevent them from entering the office network.
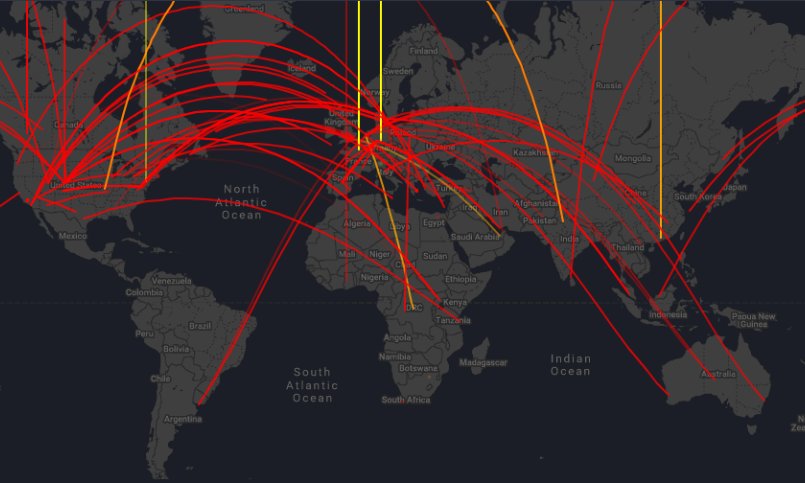
From these "malicious" addresses a multitude of different types of attacks (spam, scanners, Windows exploits, proxies, botnets, phishing, web attacks) are produced. A few years ago these cyber-attacks mainly came from the USA, but in recent years this has changed and they now come from Russia and China.
Another source of problems comes from malicious web addresses. According to market sources, more than 25% of the websites on the internet are infected (malware, proxy, phishing, botnets, spyware and adware). So if we are not careful, it is easy to fall into one of them.
The problem of "phishing" is particularly relevant, as in this case the website of a well-known company (UPS, Microsoft, Apple, Dropbox, Facebook, banks, etc.) is spoofed in order to trick the user into accessing their credentials.

Such infections can also be controlled with a state-of-the-art firewall that prevents, in real time, access to disreputable websites.
However, the general problem for SMEs is that they have neither the financial nor the human resources to deal with these problems. But their lives depend on it. According to American market sources, about 60% of SMEs that were not prepared to deal with these threats close down within 6 months of being attacked!
Imagine what would happen if someone broke into your company's network and deleted all your customer information, offers, projects/ordering in progress, accounting, etc. A disaster!
This is why we are introducing the solutions of the American manufacturer Untangle to the Spanish market. This company has an intelligent threat information system in the network. Here we can see a detail of cyber-attacks in real time:
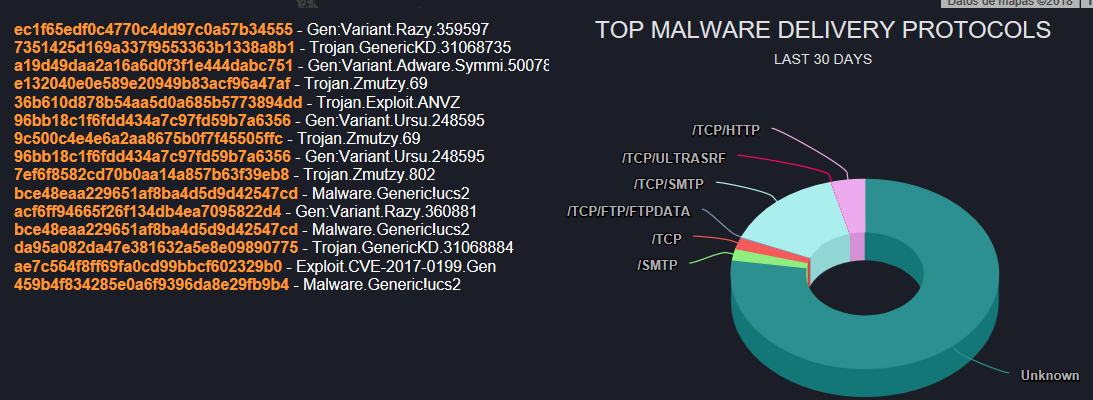
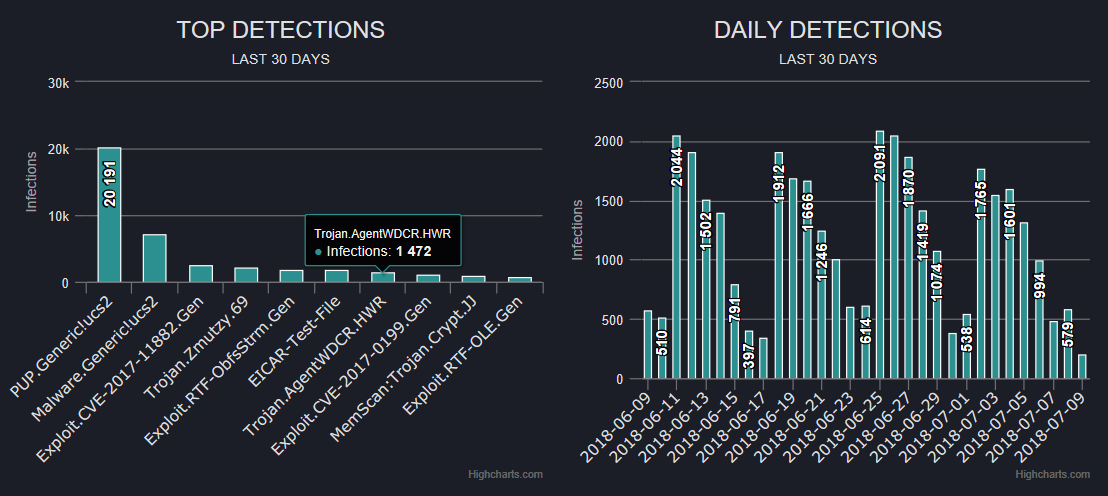
Some of this information, among others, is used to define strategies for the control of cyber security in our offices.
In addition, these solutions are specially designed to minimise the economic and resource impact required for their deployment in SMEs. They can even be deployed in the cloud, without having to install anything in each branch/office or workshop.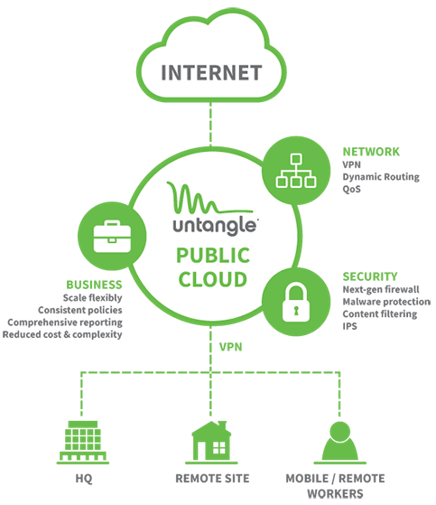
Their costs are very low and in a simple way they allow the SME to establish a "smart" barrier against all cyber-attacks, both in its main office and for its branches or remote users who telework.
At Aplicaziones we offer to carry out a study, without obligation, on the "best practices" in cybersecurity that we recommend for your company and advise you on the implementation of Untangle that best suits your business.
More information can be found sending an email at